A Silent Risk: How Information Breaches Endanger Your Confidentiality

In the current interconnected world, data breaches have become a shockingly prevalent occurrence, posing grave risks to our individual privacy and security. Daily, millions of individuals unwittingly put their private information at stake, from financial details to private communications. These breaches are not merely a nuisance; they can lead to theft of identity, financial loss, and enduring ramifications for the victims. Understanding the mechanisms behind these breaches is crucial to safeguarding our data and maintaining our privacy.
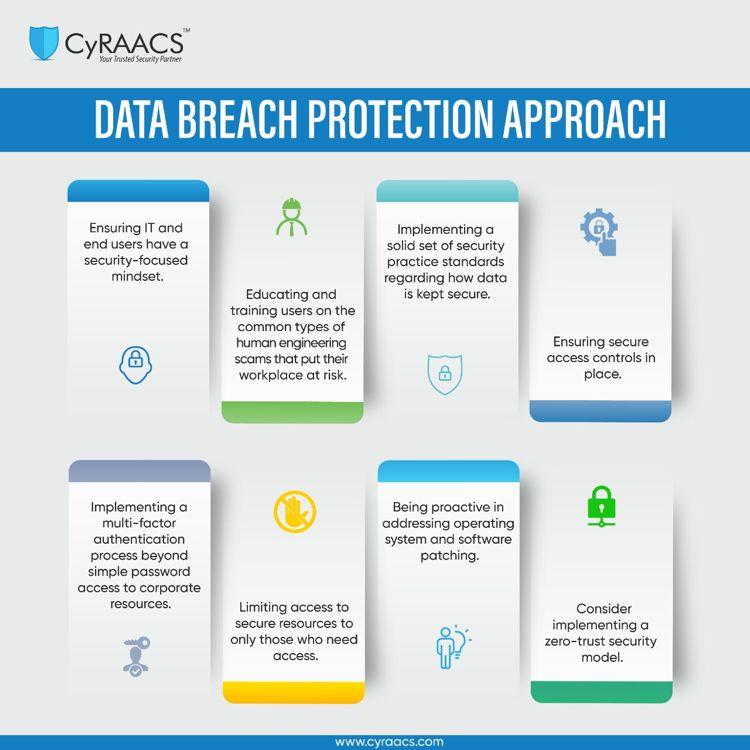
As we navigate the complex landscape of cybersecurity threats, breach prevention strategies are essential. Organizations must be proactive in implementing robust data protection measures, ensuring that their systems are fortified against potential attacks. However, even the best defenses may not be foolproof, which is why having a thorough breach response plan is important. By educating ourselves about data breaches and actively working to protect our information, we can mitigate the risks and take control of our personal privacy in this digital age.
Understanding Data Compromises
Data compromises arise if unapproved individuals are granted access to confidential information, often leading to the revelation of sensitive data such as individual names, addresses, social security numbers, and banking information. Such incidents are likely to happen to all organization, regardless of size or industry, and can have disastrous effects on consumers and organizations alike. The increase in cyber threats has made it simpler for attackers to capitalize on vulnerabilities, rendering awareness and preventive measures vitally important for defending information.
Breach prevention involves putting in place strong security measures to shield sensitive data from cyber attackers. This includes the use of ciphering, complex passwords, and regular software updates to remove weaknesses in systems. Employees should also be trained to identify phishing schemes and other common tactics used by cybercriminals. A proactive approach to cybersecurity can substantially reduce the likelihood of a data breach and help maintain the integrity of sensitive and corporate data.
As soon as a data breach happens, a swift and effective breach response is crucial to reduce damage. Organizations should have a comprehensive incident response plan in place that details the steps to take following a breach, including notifying for affected individuals and regulatory bodies. Openness is critical, as it helps foster trust while guaranteeing that those impacted can take necessary actions to protect themselves from theft of identity or additional repercussions associated with the leakage of their private information.
Avoiding Incidents: Optimal Strategies
Implementing strong password protocols is crucial for avoiding data breaches. Users should create strong passwords that consist of a combination of uppercase and small letters, numbers, and symbols. Additionally, using unique passwords for different accounts reduces the risk of a breach affecting multiple platforms. Enabling two-factor authentication provides an extra layer of security by demanding users to authenticate their identity through a supplementary method, dramatically reducing the risk of unauthorized access.
Consistently updating software and systems is another important practice in breach avoidance. online forensic science exploit vulnerabilities in outdated software, making it essential for organizations to install patches and updates quickly. This comprises not only operating systems but also applications and security tools. By sustaining an updated technology environment, businesses can safeguard confidential data from being exposed.
Employee training and awareness serve a significant role in data safeguarding. Organizations should perform periodic training sessions to educate staff about the significance of cybersecurity and best practices, such as recognizing phishing attempts and processing sensitive information. Promoting a culture of security awareness helps that employees are alert and proactive in detecting potential breaches, creating a more robust overall defense against cyber threats.
Responding to a Data Breach
Reacting properly to a breach of data is crucial in mitigating its impact on individuals and entities alike. The first step in incident response is to quickly determine the source and scope of the incident. This often entails assembling a team of cybersecurity professionals who can analyze affected systems and data. Once the incident is confirmed, it is crucial to contain the threat to stop further data loss. This may mean isolating affected systems or briefly shutting down certain operations to protect confidential information from further disclosure.
Dialogue plays a important role in how an organization handles a breach of data. It's essential to notify affected parties in a timely manner, as openness helps preserve trust and reputation. Depending on the seriousness of the incident, organizations may need to alert clients, associates, and potentially government bodies. Clear communication about what data was affected, the potential threats involved, and the steps being taken to resolve the situation can aid greatly in managing the aftermath of a data incident.
After the initial action to a data breach, organizations must focus on sustainable strategies for preventing future breaches and improved information security. This includes conducting a comprehensive investigation to understand how the incident occurred, updating security protocols, and investing in training for staff to recognize security threats. By learning from the event and strengthening defenses, organizations can better protect themselves and their stakeholders from subsequent incidents.
